Sofort lieferbar (Download)
Johnny Long's last book sold 12, 000 units worldwide. Kevin Mitnick's last book sold 40, 000 units in North America.
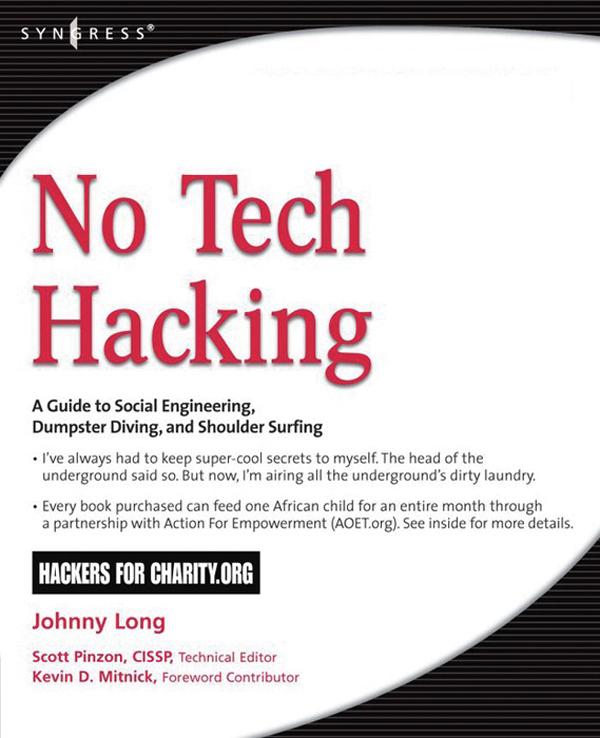
As the cliché goes, information is power. In this age of technology, an increasing majority of the world's information is stored electronically. It makes sense then that we rely on high-tech electronic protection systems to guard that information. As professional hackers, Johnny Long and Kevin Mitnick get paid to uncover weaknesses in those systems and exploit them. Whether breaking into buildings or slipping past industrial-grade firewalls, their goal has always been the same: extract the information using any means necessary. After hundreds of jobs, they have discovered the secrets to bypassing every conceivable high-tech security system. This book reveals those secrets; as the title suggests, it has nothing to do with high technology.
. Dumpster Diving
Be a good sport and don't read the two "D words written in big bold letters above, and act surprised when I tell you hackers can accomplish this without relying on a single bit of technology (punny).
. Tailgating
Hackers and ninja both like wearing black, and they do share the ability to slip inside a building and blend with the shadows.
. Shoulder Surfing
If you like having a screen on your laptop so you can see what you're working on, don't read this chapter.
. Physical Security
Locks are serious business and lock technicians are true engineers, most backed with years of hands-on experience. But what happens when you take the age-old respected profession of the locksmith and sprinkle it with hacker ingenuity?
. Social Engineering with Jack Wiles
Jack has trained hundreds of federal agents, corporate attorneys, CEOs and internal auditors on computer crime and security-related topics. His unforgettable presentations are filled with three decades of personal "war stories" from the trenches of Information Security and Physical Security.
. Google Hacking
A hacker doesn't even need his own computer to do the necessary research. If he can make it to a public library, Kinko's or Internet cafe, he can use Google to process all that data into something useful.
. P2P Hacking
Let's assume a guy has no budget, no commercial hacking software, no support from organized crime and no fancy gear. With all those restrictions, is this guy still a threat to you? Have a look at this chapter and judge for yourself.
. People Watching
Skilled people watchers can learn a whole lot in just a few quick glances. In this chapter we'll take a look at a few examples of the types of things that draws a no-tech hacker's eye.
. Kiosks
What happens when a kiosk is more than a kiosk? What happens when the kiosk holds airline passenger information? What if the kiosk holds confidential patient information? What if the kiosk holds cash?
. Vehicle Surveillance
Most people don't realize that some of the most thrilling vehicular espionage happens when the cars aren't moving at all!
As the cliché goes, information is power. In this age of technology, an increasing majority of the world's information is stored electronically. It makes sense then that we rely on high-tech electronic protection systems to guard that information. As professional hackers, Johnny Long and Kevin Mitnick get paid to uncover weaknesses in those systems and exploit them. Whether breaking into buildings or slipping past industrial-grade firewalls, their goal has always been the same: extract the information using any means necessary. After hundreds of jobs, they have discovered the secrets to bypassing every conceivable high-tech security system. This book reveals those secrets; as the title suggests, it has nothing to do with high technology.
. Dumpster Diving
Be a good sport and don't read the two "D words written in big bold letters above, and act surprised when I tell you hackers can accomplish this without relying on a single bit of technology (punny).
. Tailgating
Hackers and ninja both like wearing black, and they do share the ability to slip inside a building and blend with the shadows.
. Shoulder Surfing
If you like having a screen on your laptop so you can see what you're working on, don't read this chapter.
. Physical Security
Locks are serious business and lock technicians are true engineers, most backed with years of hands-on experience. But what happens when you take the age-old respected profession of the locksmith and sprinkle it with hacker ingenuity?
. Social Engineering with Jack Wiles
Jack has trained hundreds of federal agents, corporate attorneys, CEOs and internal auditors on computer crime and security-related topics. His unforgettable presentations are filled with three decades of personal "war stories" from the trenches of Information Security and Physical Security.
. Google Hacking
A hacker doesn't even need his own computer to do the necessary research. If he can make it to a public library, Kinko's or Internet cafe, he can use Google to process all that data into something useful.
. P2P Hacking
Let's assume a guy has no budget, no commercial hacking software, no support from organized crime and no fancy gear. With all those restrictions, is this guy still a threat to you? Have a look at this chapter and judge for yourself.
. People Watching
Skilled people watchers can learn a whole lot in just a few quick glances. In this chapter we'll take a look at a few examples of the types of things that draws a no-tech hacker's eye.
. Kiosks
What happens when a kiosk is more than a kiosk? What happens when the kiosk holds airline passenger information? What if the kiosk holds confidential patient information? What if the kiosk holds cash?
. Vehicle Surveillance
Most people don't realize that some of the most thrilling vehicular espionage happens when the cars aren't moving at all!
Inhaltsverzeichnis
1;Front Cover;1 2;No Tech Hacking: A Guide to Social Engineering, Dumpster Diving, and Shoulder Surfing;2 3;Copyright Page;4 4;Johnny Long, Author;6 4.1;Im Johnny. I Hack Stuff.;6 5;Technical Editor;8 6;Contributing Author;9 7;Foreword Contributor;10 8;Special Contributors;11 9;Contents;14 10;Foreword;18 11;Introduction;20 11.1;What Is No-Tech Hacking?;20 12;Chapter 1: Dumpster Diving;26 12.1;Introduction to Dumpster Diving;27 13;Chapter 2: Tailgating;38 13.1;Introduction to Tailgating;39 13.1.1;Dressing the Part;42 13.1.2;Real-World Tailgating Exercise;49 14;Chapter 3: Shoulder Surfing;52 14.1;What is Shoulder Surfing?;53 14.2;Outside of the box;55 14.3;Great Locations for Should Surfing;58 14.4;Electronic Deduction;64 14.5;Killer Real-Life Surfing Sessions;72 14.5.1;Military Intelligence;72 14.5.2;Airliner Espionage;75 14.5.3;Robbing a Bank;78 14.5.4;Robbing Banks in Uganda, Africa;83 15;Chapte 4: Physical Security;86 15.1;Introduction;87 15.2;Lock Bumping;87 15.2.1;Shimming Padlocks (With Deviant Ollam);88 15.2.2;Master Lock Combo Lock Brute Forcing;92 15.2.3;Toilet Paper vs. Tubular Locks;97 15.2.4;Electric Flossers: A Low-Tech Classic;98 15.2.5;Laptop Locks Defeated by Beer (With Matt Fiddler and Marc Weber Tobias);100 15.2.6;TSA Locks (With Marc Weber Tobias);103 15.2.7;Gun Trigger Locks vs. Drinking Straw (With Marc Tobias and Matt Fiddler);105 15.2.8;Entry Techniques: Loiding (aka the Old Credit Card Trick);108 15.2.9;Entry Techniques: Motion Sensor Activation;112 15.2.10;Bypassing Passive Infrared (PIR) Motion Sensors;115 15.2.11;Camera Flaring;117 15.2.12;Real World: Airport Restricted Area Simplex Lock Bypass;121 16;Cahpter 5: Social Engineering: Here's How I Broke Into Their Buildings;126 16.1;Introduction;127 16.2;How Easy Is It?;127 16.3;Human Nature, Human Weakness;130 16.3.1;Hello? Is this thing on?;131 16.4;The Mind of a Victim;133 16.4.1;"Social engineering would never work against our company!";133 16.4.2;What Was I Able to Social Engineer Out of
Mary?;135 16.4.3;The Final Sting;135 16.4.4;Why did this scam work?;136 16.5;Countering Social Engineering Attacks;137 16.5.1;Be Willing To Ask Questions;137 16.5.2;Security Awareness Training;138 16.5.2.1;Posters;138 16.5.2.2;Videos;140 16.5.3;Certificates;142 17;Chapter 6: Google Hacking Showcase;146 17.1;Introduction to the Introduction;147 17.2;Introduction;147 17.3;Geek Stuff;148 17.3.1;Utilities;148 17.3.2;Open Network Devices;153 17.3.3;Open Applications;162 17.4;Cameras;168 17.5;Telco Gear;178 17.6;Power;185 17.7;Sensitive Info;191 17.7.1;Police Reports;200 17.8;Social Security Numbers;204 17.8.1;Credit Card Information;210 17.9;Beyond Google;215 17.10;Summary;220 18;Chapter 7: P2P Hacking;222 18.1;Understanding P2P Hacking;223 18.2;Real World P2P Hacking: The Case of the Naughty Chiropractor;237 19;Chapter 8: People Watching;242 19.1;How to "People Watch";243 20;Chapter 9: Kiosks;252 20.1;Understanding Kiosk Hacking;253 20.2;Real World: ATM Hacking;264 21;Chapter 10: Vehicle Surveillance;270 21.1;How Easy Is Vehicle Surveillance?;271 22;Chapter 11: Badge Surveillance;284 22.1;Where Are Your Badges?;285 22.2;Electronic Badge Authentication;289 22.3;Real World Badge Surveillance;291 23;Epiloque: Top Ten Ways to Shut Down No-Tech Hackers;298 23.1;Go Undercover;299 23.2;Shred Everything;299 23.3;Get Decent Locks;300 23.4;Put that Badge Away;301 23.5;Check Your Surveillance Gear;301 23.6;Shut Down Shoulder Surfers;302 23.7;Block Tailgaters;302 23.8;Clean your Car;303 23.8.1;Watch your Back Online;304 23.9;Beware of Social Engineers;304 24;Index;306
Mary?;135 16.4.3;The Final Sting;135 16.4.4;Why did this scam work?;136 16.5;Countering Social Engineering Attacks;137 16.5.1;Be Willing To Ask Questions;137 16.5.2;Security Awareness Training;138 16.5.2.1;Posters;138 16.5.2.2;Videos;140 16.5.3;Certificates;142 17;Chapter 6: Google Hacking Showcase;146 17.1;Introduction to the Introduction;147 17.2;Introduction;147 17.3;Geek Stuff;148 17.3.1;Utilities;148 17.3.2;Open Network Devices;153 17.3.3;Open Applications;162 17.4;Cameras;168 17.5;Telco Gear;178 17.6;Power;185 17.7;Sensitive Info;191 17.7.1;Police Reports;200 17.8;Social Security Numbers;204 17.8.1;Credit Card Information;210 17.9;Beyond Google;215 17.10;Summary;220 18;Chapter 7: P2P Hacking;222 18.1;Understanding P2P Hacking;223 18.2;Real World P2P Hacking: The Case of the Naughty Chiropractor;237 19;Chapter 8: People Watching;242 19.1;How to "People Watch";243 20;Chapter 9: Kiosks;252 20.1;Understanding Kiosk Hacking;253 20.2;Real World: ATM Hacking;264 21;Chapter 10: Vehicle Surveillance;270 21.1;How Easy Is Vehicle Surveillance?;271 22;Chapter 11: Badge Surveillance;284 22.1;Where Are Your Badges?;285 22.2;Electronic Badge Authentication;289 22.3;Real World Badge Surveillance;291 23;Epiloque: Top Ten Ways to Shut Down No-Tech Hackers;298 23.1;Go Undercover;299 23.2;Shred Everything;299 23.3;Get Decent Locks;300 23.4;Put that Badge Away;301 23.5;Check Your Surveillance Gear;301 23.6;Shut Down Shoulder Surfers;302 23.7;Block Tailgaters;302 23.8;Clean your Car;303 23.8.1;Watch your Back Online;304 23.9;Beware of Social Engineers;304 24;Index;306
Produktdetails
Erscheinungsdatum
18. April 2011
Sprache
englisch
Seitenanzahl
384
Autor/Autorin
Johnny Long
Verlag/Hersteller
Kopierschutz
mit Wasserzeichen versehen
Produktart
EBOOK
Dateiformat
EPUB
ISBN
9780080558752
Entdecken Sie mehr
Bewertungen
0 Bewertungen
Es wurden noch keine Bewertungen abgegeben. Schreiben Sie die erste Bewertung zu "No Tech Hacking" und helfen Sie damit anderen bei der Kaufentscheidung.









